27373
27373
With Microsoft Entra ID Single Sign-on, you can allow your agents and customers to log in to the respective HappyFox panels (Agent Portal and Customer Portal) with their Entra ID credentials.
Note:
-
The Administrator in Entra ID needs to set up this integration (needs access to Active Directory / Application settings)
-
Customers/Users are expected to login into the contact portal and agent members are expected to login into agent portal. The right URL should be shared with concerned parties.
-
Agents logging in for the first time will need to be approved by an administrator from the Manage > Pending SSO Agents tab.
-
The custom domain in HappyFox (if present) needs to be SSL enabled in order to work with Entra ID integration.
- Integration can be achieved for all Entra ID active directory plans(including trial account)
Enabling Microsoft Entra ID SSO involves:
- Configuring the HappyFox enterprise app inside your Microsoft Entra ID account.
- Installing the Entra ID SSO app inside HappyFox with the target URL and IdP Signature.
Configuring HappyFox enterprise app inside your Microsoft Entra ID:
1. Login to Microsoft Entra ID. Choose "Entra ID" and click on "Enterprise applications".

2. Click on "New Application".

3. Navigate to "CRM" category and search for "HappyFox".

4. Select “Add" to confirm adding HappyFox. You can customize the name and icon if required.

5. After adding HappyFox, navigate back into "Enterprise Applications" and click on the Name entered by you in the previous step (here "HappyFox two")
6. Now, navigate to the "Single-Sign-On" tab. For Single Sign-on Mode, choose "SAML"

7. Under Basic SAML Configuration, the following needs to be filled:
Identifier (Entity ID): https://<account-name>.happyfox.com/saml/metadata/
Add the following in separate Reply URL fields:
https://<account-name>.happyfox.com/staff/saml/azure/callback/
https://<account-name>.happyfox.com/staff/saml/callback/
https://<account-name>.happyfox.com/saml/callback/
Sign On URL : https://<account-name>.happyfox.com/
Note: If SSO is being setup using Custom SAML Method app from HappyFox app catalog, then use the below values in the Enterprise Application that configured in Azure/Entra ID
Identifier (Entity ID): https://<account-name> .happyfox.com/saml/client-metadata/
Reply URL: https://<account-name>.happyfox.com/saml/azure/callback/
https://<account-name>.happyfox.com/staff/saml/callback/
https://<account-name>.happyfox.com/saml/callback/
Sign On URL : https://<account-name>.happyfox.com/
Note:
#1 - If you are using more than one SAML integration in HappyFox, then the ACS callback url for custom SAML should be https://.happyfox.com/saml/custom-saml/callback/ or https:// .happyfox.com/staff/saml/custom-saml/callback/
#2 - If you are using custom domain on your HappyFox help-desk, ensure to include the ACS url in both custom domain format and in default HappyFox url format
Note: If you have setup a custom domain URL for your HappyFox account replace <account-name>.happyfox.com in the previous URLs with your custom domain.


Examples
Sign On URL : https://xyz.happyfox.com/
Identifier : https://xyz.happyfox.com/saml/metadata/
8. Under SAML Signing Certificate, click on Edit icon. Enter the email address that needs to be notified of the setup.

The Base64 Certificate can be download directly as shown above or go to Edit icon >> Context menu.

10. Copy the “Login URL” from "Set Up HappyFox" to your clipboard that needs to be pasted on the HappyFox setup.

Assign User Permissions:
Entra ID agent/user needs to be assigned necessary permissions to the application created in Azure (here HappyFox).
To assign User permission, follow the below steps:
1. Open the Entra ID Portal and sign in as a Global Administrator or Co-admin.
2. Navigate to Enterprise Applications >> Your HappyFox set up name ( Here "HappyFox tw") >> User and Groups >> Add User.
3. Select the user who needs to be given permission and click on Assign.

Installing the Entra ID SSO app inside HappyFox with the target URL and Certificate:
- Log in to HappyFox. Go to Apps >> Single Sign On >> Azure AD.
- Click "Install".
- Ensure SAML integration is active. Under "SAML Configuration", ensure it is "Entra ID".
- SSO Target URL is the URL that was copied previously (in step #10) into the clipboard.
- Open the saved certificate (copied to clipboard in step #9), copy its content into a text editor and paste it in IdP Signature and click on Save Settings.

Test the Setup in AZURE AD:
Once the details are filled on both the Azure and HappyFox front, you can test the connection.

LOGIN SCENARIOS
For Agent portal SSO - https://<account-name>.happyfox.com/staff/saml/azure/callback/
For Contact portal SSO - https://<account-name>.happyfox.com/saml/azure/callback/
Scenario 1: Agent Login:
From the HappyFox’s agent login page, when the agent clicks choose Azure SSO as the login method, he/she gets directed to the login screen shown below:


-
When an existing agent member enters his credentials, he will be directed to the agent portal.
-
When a new agent member enters his credentials, he will be added as a pending agent member.
Scenario 2: Customer Login
From HappyFox contact login page, when the contact chooses Azure SSO as the login method, he/she gets directed to Azure login screen.

-
If an existing contact enters his credentials, he/she will be directed to the self-service portal
-
If a new customer enters his credentials, a new contact account will be created and he/she will be directed to the self-service portal
Using alternate email addresses for SSO
By default Entra ID/Azure uses the User Principal Name as the attribute to identify a logging in user. To update this to another email attribute, the following steps are to be followed.
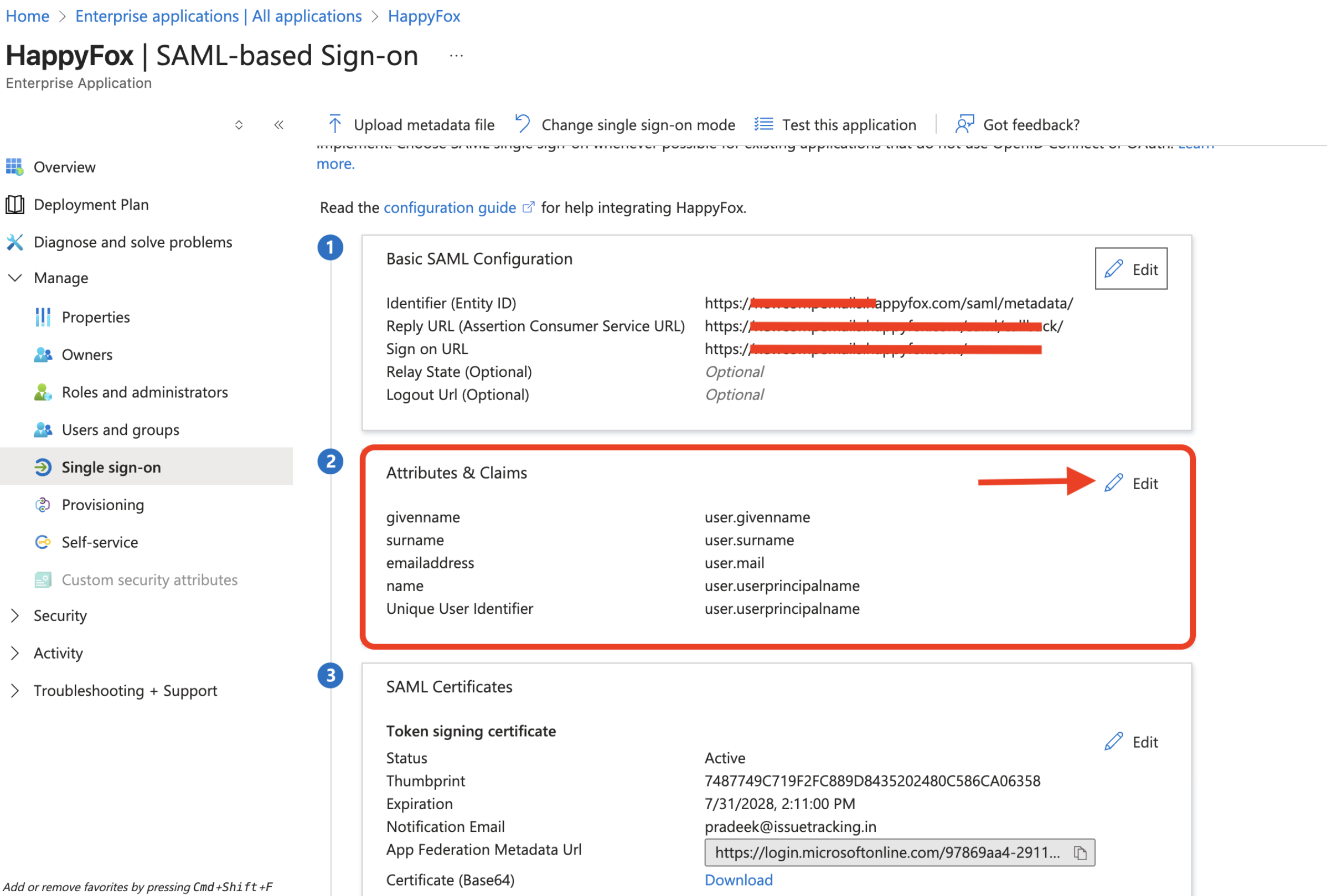
- Go to the Enterprise Application created for HappyFox
- Click Edit in Step 2 Attributes & Claims
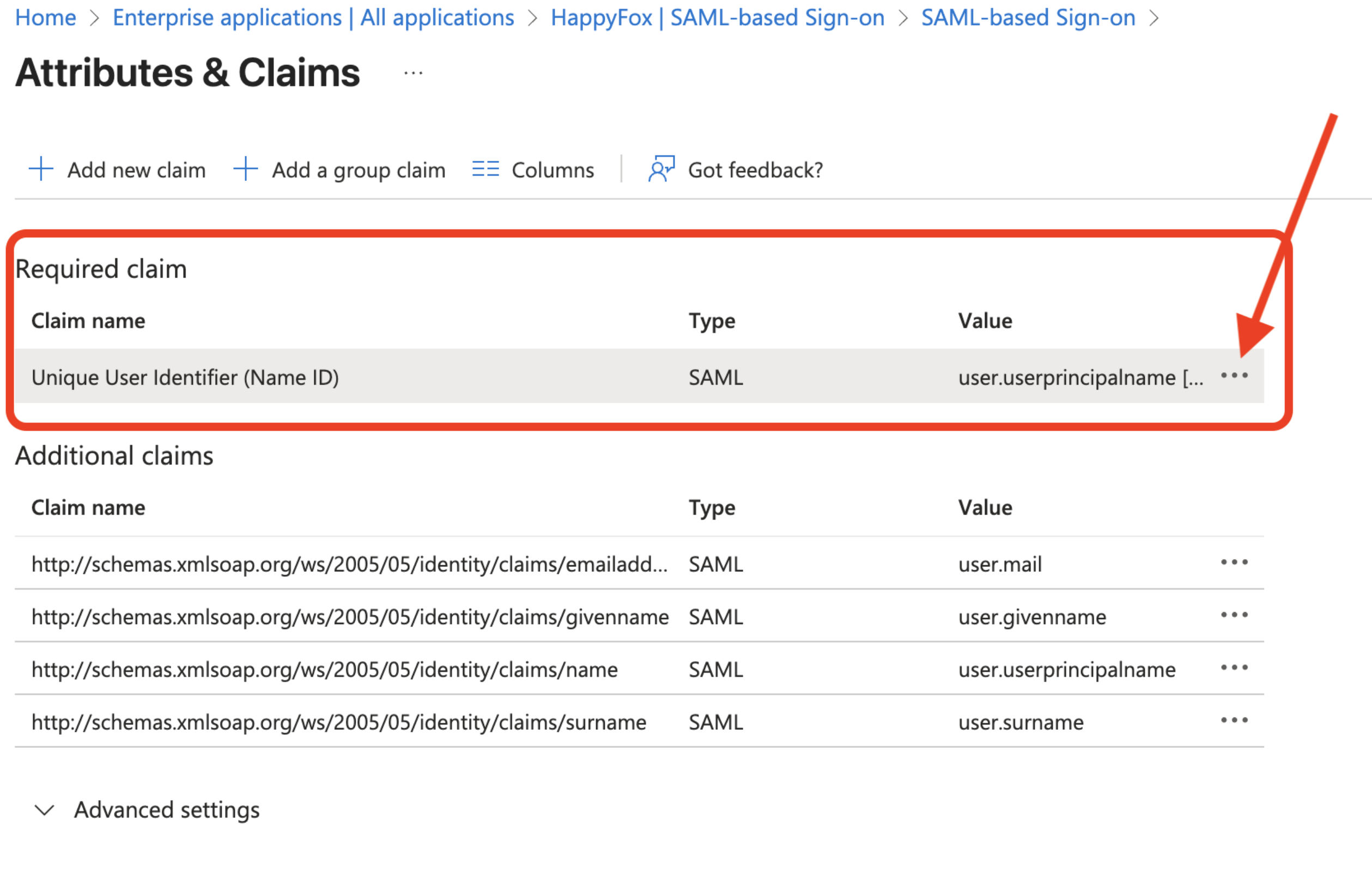
3. Click the three dots button next to the Unique User Identifier (Name ID)
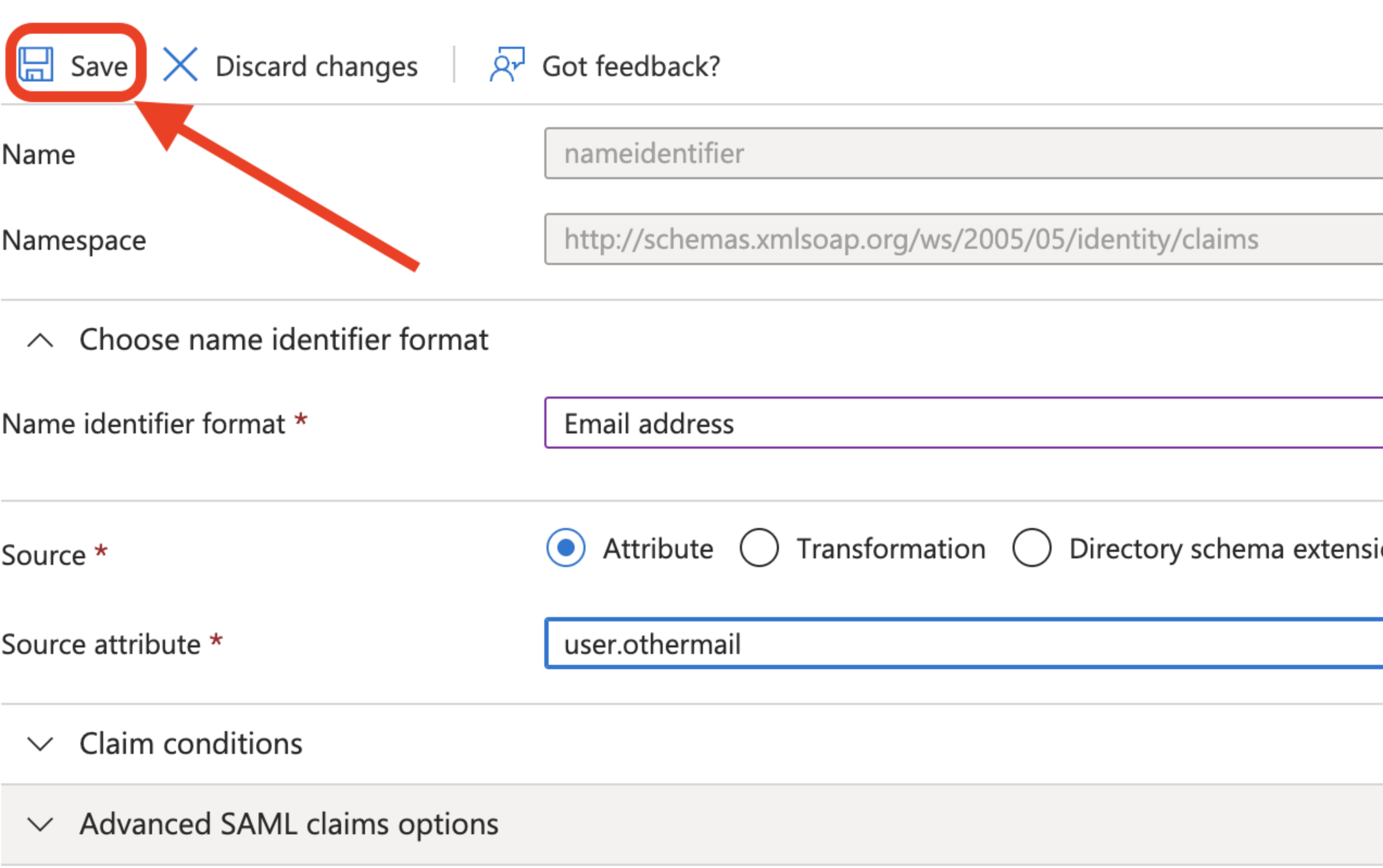
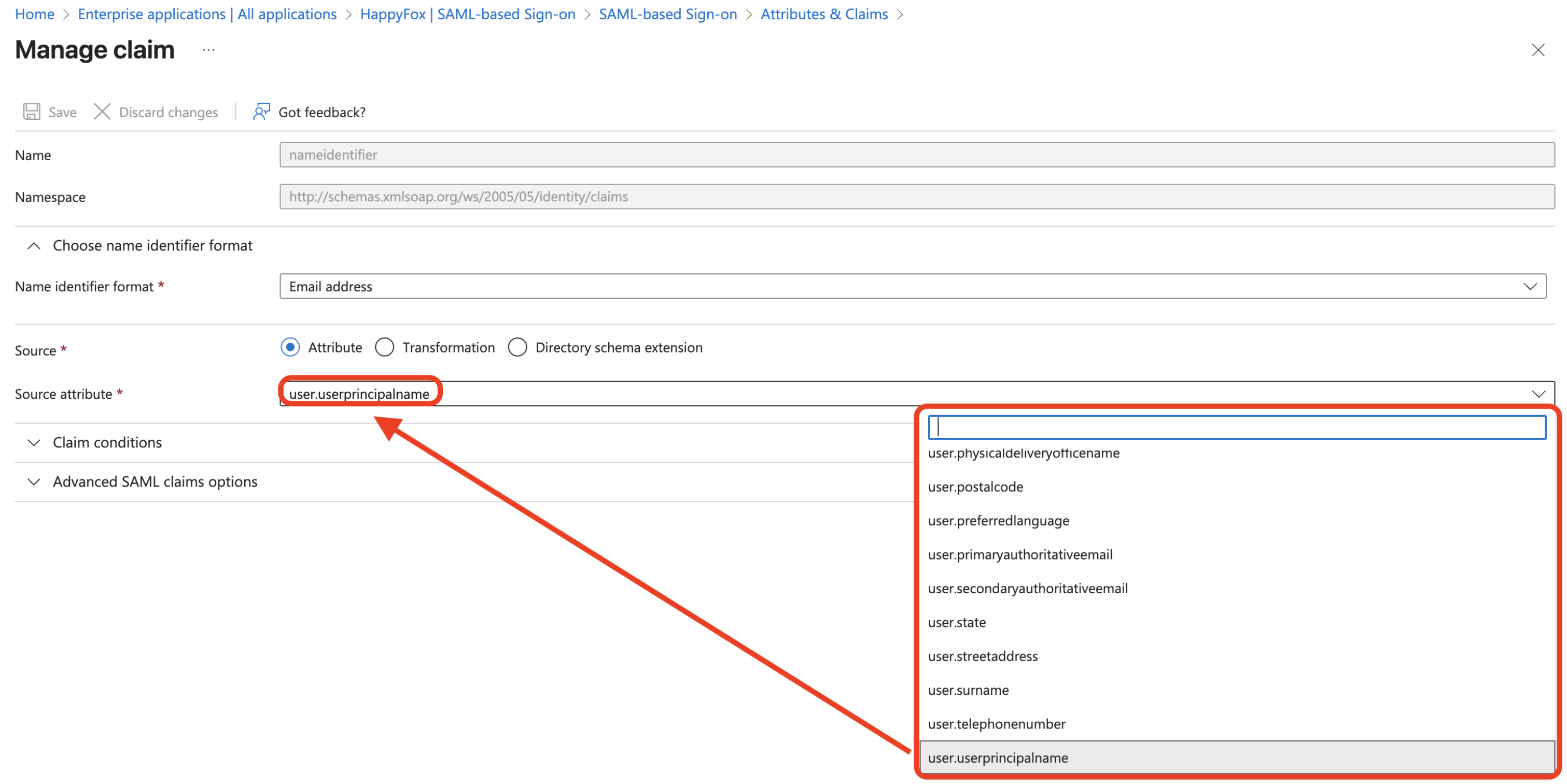
4. Update the Source attribute from user.userprincipalname to another field that carries the email address that is supposed to be sent to HappyFox
5. Once done, click Save.